Mac Network Hacking Tools
Ethical Hacking is growing faster in 2020 and everyone is just going behind it. Nowadays everyone wants to automate their works from sending email to posting on social media account. And for this activities you will require best tools or bots so that they can do automation work easily.
If you decided to choose an automation tool then you have to be very careful about the security of these tools. Because all these tools can be easily hacked by hackers if they are not coded well. And to test their strength you need good network security tools and sometimes best ethical hacking tools.
Also Check This | Top 10 Best WiFi Hacking Apps For Android Smartphone | 2020 Edition
Since Mac OS X is a UNIX based operating system, you get great tools that come natively with UNIX operating systems such as netcat and SSH. You also have powerful scripting languages installed such as Perl and Python. With all of the benefits and features of the Mac OS X, there is no reason to not use Mac OS X for your pen testing platform. Jul 27, 2017 WikiLeaks has just published a new set of classified documents linked to another CIA project, dubbed 'Imperial,' which reveals details of at least three CIA-developed hacking tools and implants designed to target computers running Apple Mac OS X and different flavours of Linux operating systems. If you are a regular reader of THN, you must be aware that this latest revelation by the. KisMACis a wireless network discovery tool for Mac OS X which is the mac version of Kismet. Although not as novice-friendly as similar applications this WiFi Hacking tool has a very popular following. Essentially THC Hydra is a fast and stable Network Login Hacking Tool that will use a dictionary or brute-force attacks to try various passwords and login combinations against a login page. This hacking tool supports a wide set of protocols including Mail (POP3, IMAP, etc.
Oct 03, 2017 Wireshark monitors network and analyzes all sent or received data packets. Passwords, personal information can be sniffed. Wireshark is one of the most popular tool in networking. Social Engineering Toolkit (SET): It is measured one of the best tool for.
Ethical hacking Tools will test their ability and strength by attacking them in many ways. With these hacking tools, you can test your network security, password strength and even your smartphone vulnerability.
So lets go further and have a look at these best ethical hacking tools.
Table of Contents
- Best Ethical Hacking Tools in 2020
Best Ethical Hacking Tools in 2020
All the hacking tools provided here are free of cost and effective. You can easily download them from the respective website and test your network security. I am just publishing this article for educational purpose and we do not promote the malicious practice.
Most of the hacking tools are made for the Linux operating system but you can also run them in Windows 10 or Mac OX by installing Virtual Machines.
1.Metasploit
Metasploit is an open-source cybersecurity project that allows you to find vulnerabilities in remote software. It is available for Linux, Windows and Mac OS operating system.
With the help of Metasploit, you can create custom exploits and test the vulnerability of a system easily. These is very popular among Kali Linux users who want to try out android phone hacking.
The Metasploit security tool can be used to detect vulnerability in system, execute remote attacks, evade detection system and to run security scans. Onedrive app download for mac free.
Supported platforms include: Mac OS X | Linux | Windows
2. John The Ripper
John The Ripper is one of the most popular password cracking tools of all the time. This tool is used to crack the password of any operatig system and remote files easily.
It has the ability to detect the algorithm use to encrypt the password and prepare itself accordingly. This ability make its one of the intelligent password cracking tools and a good choice for ethical hackers.
These ethical hacking tools use the brute force technique to decrypt the password and algorithm such as:
- DES, MD5, Blowfish
- Kerberos AFS
- Hash LM (Lan Manager), the system used in Windows NT / 2000 / XP / 2003
- MD4, LDAP, MySQL (using third-party modules)

Supported platforms include: Mac OS X | Linux | Windows
3. NMAP
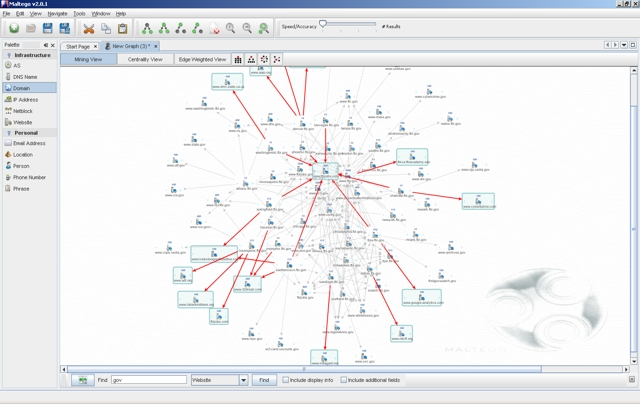
NMAP is an open source security auditing tool which can be easily used by beginners on any operating system. Nmap (Network Mapper) is used for the network exploration and to scan the large networks easily.
It can see all the host connect in network and what application they are running and even which operating system thet are using. Nmap creates a map of those hosts and present them in graphical as well as simple map form.
Nmap uses the IP packets in novel way to determine the available host on the network. It is one of the most effective network mapper available on the internet.
It can do the following task for you:
- Audit device security
- Detect open ports on remote hosts
- Network mapping and enumeration
- Find vulnerabilities inside any network
- Launch massive DNS queries against domains and subdomains
Supported platforms include: Mac OS X | Linux | Windows
4. Wireshark
Wireshark is a GTK+ based network protocol analyzer. It is also an open source project which is used to intercept and analyze the network in real-time.
With the sniffing technology, one can easily intercept and loads the network packet in human-readable formats. You can also use wireshark to monitor wifi network and to monitor packets which are transmitting over the network.
Also Read |GBWhatsApp Apk Download Latest Version 8.25 AntiBan | 2020
You can easily load them and know the password of any wifi network. Wireshark supports up to 2000 different network protocols, and is available on all major operating systems .
Main Features of Wireshark:
- Saves analysis for offline inspection
- Packet browser
- Powerful GUI
- Rich VoIP analysis
- Inspects and decompresses gzip files
- Reads other capture files formats including: Sniffer Pro, tcpdump (libpcap), Microsoft network monitor, Cisco Secure IDS iplog, etc.
- Supported ports and network devices: Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI.
- Protocol decryption includes but not limited to IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Exports results to XML, PostScript, CSV, or plain text
5. Nikto
Nikto is another well known ethical hacking tool which is also a part of Kali Linux Distribution. It is also available in many other Linux Distribution like Fedora.
It is very simple and easy to use hacking tool due to its simple command line. Nikto is used to scan web server and perform a different type of test against the remote host. This tool can easily scan the base configuration file in any operating system or web server.
It can also tell you whether the server has multiple index files, HTTP Server options, etc
1.Download Hungry Shark Evolution Hack Tool Installer. 2.Run the installer (is installer because we can update the hack when it’s needed ). 3.Run the executable from the desktop. 4.Select your device platform and press “Detect device” button. After that enter the amount of resources and press “Start Hack” button. Hacking tool for hungry shark evolution. If you are looking for Hungry Shark Evolution hack tool but you are very difficult to find on the internet do not worry friends, you can get a Hungry Shark Evolution hack the Unlimited Coins and Gems. This tool will create a generator that will produce unlimited items. Hack This tool is clean of viruses and you can use it safely. Our soft works on all Android and iOS devices. It does not require any jailbreak or root. Download Hungry Shark Evolution Hack Tool full version. Official Hungry Shark Evolution Hack Tool is ready to work on iOS, MacOS and Android. From Gamesintosh.com Website Managing 75+ levels and each of the one by one, appears like excessively exhausting.
Nikto’s main features include:
- Detects default installation files on any OS
- Detects outdated software applications.
- Runs XSS vulnerability tests
- Launches dictionary-based brute force attacks
- Exports results into plain text, CSV or HTML files
- Intrusion detection system evasion with LibWhisker
- Integration with Metasploit Framework
Supported platforms include: Linux | Fedora
6. SQLNinja
SQLNinja is a SQL vulnerability scanner bundled with Kali Linux distribution. This tool is dedicated to target and exploit web apps that use MS SQL Server as the backend database server.
Using SQLNinja you can:
- Test database schema
- Fingerprint remote database
- Brute force attack with a word list
- Direct shell & reverse shell
Supported platforms include: Linux | Mac OS X | Free BSD
7. Acunetix
Acunetix is an automated network security and ethical hacking tool which is use to audit your web application by checking vulnerabilites like SQL injection, cross site scripting and other exploitable vulnerabilities.
Basically it is used to scan any website or a web application that can be easily accessed by any web browser through HTTP or HTTPS protocol.
It is a strong solution for analyzing the vulnerabilities in web applications which inculde JAVA, Ajax, SQL. It has an advanced crawler which can find any files in this type of web application to test their vulnerability.
8. Aircrack-ng
Aircrack-ng is one of the best favorite ethical hacking tools to crack the WiFi passwords. I personally use these to test my WiFi vulnerability in different protocols including WEP and WPA.
It includes full support for 802.11 WEP and WPA-PSK networks and works by capturing network packets. It then analyzes and uses them to crack Wifi access.
In these network tool, you can monitor packet which is transmitting between your WiFi and connected devices and easily carck the wifi password by a brute-force attack. It is one of the best tools for hacking WiFi passwords.
Main features of Aircrack-ng:
- Extensive documentation (wiki, manpages)
- Active community (forums and IRC channels)
- Support for Linux, Mac and Windows Wifi detection
- Launches PTW, WEP and Fragmentation attacks
- Supports WPA Migration Mode
- Fast cracking speed
- Multiple Wifi card support
- Integration with 3rd party tools
9. Kismet
Kismet is a network detector, sniffer and an intrusion detection system that is used to keep an eye on the packets transmitting over a WiFi network. It works on all network adapters which support monitor mode.
And can sniff 802.11a, 802.11b, 802.11g, and 802.11n traffic. If your network adapter does not support monitor mode then it time to update that. You can try out TP-Link WN227, which is very cheaper and a good choice for kali Linux users.
Must Read |Best USB WiFi Adapter Compatible with Kali Linux for Penetration Testing
Supported platforms include: Linux, FreeBSD, NetBSD, OpenBSD, and Mac OS X
10. Social Engineering Toolkit
Social-Engineer Toolkit is an advanced framework for simulating multiple types of social engineering attacks like credential harvestings, phishing attacks, and more.
Best Hacking Tools For Mac
If you want to make a clone of social sites like Facebook, twitter and try to attack on friends social account then the hacking tool will help you. It will create a clone of any website under one minute and can harvest their email id and passwords easily.
Mac Network Hacking Tools List
This Python-driven tool is the standard tool for social engineering penetration tests with more than two million downloads. It automates the attacks and generates disguising emails, malicious web pages and more.
Supported platforms include: Linux and Mac OS X
Wrapping Up
Pc Hacking Programs
There are numbers of Ethical Hacking Tools are available on the internet which are used by many professionals to test the vulnerabilities in the network. If you want to learn ethical hacking you can start using these tools.
Macos Hacking Tools
But be aware there are also many tools which are infected with the virus and you should be aware of them. So always download these tools from official websites.