Shows Wrong Device Name Mac Hacked
Find your computer’s name and network address on Mac. If other people want to locate your Mac on the network, they need to know your computer’s name or network address. Your Mac has several identifiers that people may look for on the network: computer name, local hostname (or local network name), and network address. Open Sharing.
- Google Calendar is the official calendar for Android devices that has been tested out by many users around the globe. If you are right now trying to get away from it, consider changing your mind. Since this application is installed on most Android devices by default, many users think that there is nothing special in this program. They are wrong.
- This table identifies all devices connected to the router by the device name, IP address and MAC address. On a Netgear router, click the “Attached Devices” link in the left navigation panel under the Maintenance heading.
For most of us, our phones are the center of our daily lives, and as a result, they contain a treasure trove of personal information, from banking details to messaging and email accounts. This sensitive data can be pretty enticing to a range of the nefarious, from cybercriminals to someone you may even know.
Phone hacking can involve the unknowing download of spyware that relays information on your activity – such as logging keystrokes to scrape passwords; spy apps downloaded by someone with access to your device; or other malware that exploits your phone, for example by using its internet bandwidth in a botnet, as occurred with malware that infected nearly 20 million Android devices.
“The most common way that smartphones can be hacked is to infect the device with malware,” says Victor Chebyshev, a security researcher at Kaspersky Lab. This malware can arrive on the device buried inside apps downloaded by the user – and the likelihood of a malicious app rises when downloading away from the official app stores, which police their content.
While iPhones aren’t immune to hacking, Apple’s strict vetting policy means the incidence of bad apps targeting iPhones (at least non-jailbroken ones) is lower than for Android phones. “Android devices are more susceptible to these kinds of attacks because they have the option to install applications from third parties,” says Chebyshev.
9 steps to figuring out who hacked your phone
A sluggish phone or fast-draining battery are common symptoms of a compromised phone – but they can also indicate your device needs a spring clean to spruce up performance or improve its battery life. Another red flag is if your data usage has gone through the roof – this could indicate a dodgy app is sending data back to its mothership.
“Whether a user can determine who is responsible for a compromised phone depends on what kind of threat was on the device,” says Chebyshev.
According to Verizon’s 2020 Data Breach Investigation, 86% of cyberattacks are motivated by monetary gain – for example, through selling someone’s stolen credentials on the dark web, gaining access to financial accounts, or hacking sensitive data and holding the victim to ransom. In these cases, hackers usually rely on malware that remotely exploits vulnerabilities in apps or operating systems to steal information (or in the case of phishing malware, trick people into inputting their critical data).
However, somebody known to you who wants to monitor your movements – whether that’s a disgruntled ex or suspicious parent – and who has physical access to your device might also be able to install a spy app that acts like malicious software, tracking your location, photos, messages and calls.
To narrow down the field of suspects, you can try to determine exactly how your phone is being compromised.
1. Check your phone bill
Are you being charged for premium-rate texts you never sent – or texts you never signed up for? You’ve probably been infected by malware that forces your phone to send or receive texts that generate revenue for cybercriminals. This common form of mobile malware is believed to be the first type found targeting Android, back in 2010, and today plenty of it is still floating around.
If you’re receiving premium-rate text messages, try texting STOP to the number. If this doesn’t work, you’ll have to contact your cell carrier who should be able to block the number.
If your phone is sending the texts, you may be able to fix it by running a security app such as Bitdefender or McAfee to find and remove malware (on Android only; security apps for iOS don’t have this feature). Also, try deleting any third-party messaging apps and any other apps you installed just before the phone started sending the texts.
2. Go through your apps list
If there are any apps you don’t remember downloading, look them up online to see if any of them have been reviewed negatively for malware or other suspicious activity. In this case, the apps will have been compromised by a hacker who likely isn’t targeting you personally but is distributing malware with the aim of scraping as much data as possible. The BankBot malware, for instance, is a trojan that has infected hundreds of Android apps to display a phishing screen to steal users’ banking credentials.
“If it was a regular trojan [malware coded within another app] the user will not be able to attribute who was responsible for the attack,” says Chebyshev. “If it was commercial spyware, it’s sometimes possible to figure out the responsible person.”
3. Look up your flashlight and battery-saver apps
Got a phone full of apps and can’t remember for sure which you downloaded? Some categories of apps have attracted more than their fair share of malicious actors – several flashlight apps on Google Play were infected with malware that tried to scrape users’ financial info, while one should be wary of battery-saver apps as they have often been used for malware, says Josh Galindo, director of training at phone repair service uBreakiFix.

If you have these types of apps, check online for any negative reviews. You can also try deleting them to see if this affects your phone performance. “If you install an app and the device performance decreases, that’s an indicator,” says Galindo. “If you uninstall the app and your device begins working properly again, this means that the app is likely contaminated with malware and you should avoid downloading it in the future.”
4. Double-check your favorite popular games
Downloaded a new super-popular game recently? Ensure it operates like it’s meant to – and validate that by looking up reviews online – otherwise it may be a scam version, potentially ridden with cryptojacking malware.
Cryptojacking trojans mine cryptocurrency unbeknownst to users, and their prevalence has risen on smartphones that when infected in thousands, can deliver attackers a high overall processing power. The idea is that, if a cryptojacker hacks other devices, they can get paid for mining without having to use their own resources (or pay the electricity bill).
On mobile, cryptojacking malware tends to hide inside innocent-looking apps such as fake versions of popular games. If your phone slows down, heats up and its battery is dying long before the end of the day – and you’ve tried to improve your battery life– it could be a sign that a malicious app like a cryptojacking trojan is hogging all the juice.
They’re mostly prevalent on Android – and if you’ve downloaded from non-official app marketplaces, the risk is higher.
5. Scroll through your call list
Done all of the above and still convinced that someone somewhere has your personal data, siphoned from your smartphone? Apps aren’t the only way a phone can be infected by malware. Have you picked up any random calls lately? “Callers offering a free cruise or claiming that you won a sweepstakes are likely scam efforts to hack your information or record your voice,” says Galindo.
6. Did you click that link?
If you recently clicked on a link on a text message or an unexpected pop-up, you may have inadvertently fallen prey to phishing. Phishing often preys on panic or high emotion – as in the coronavirus-related scam texts claiming that receivers had been exposed to someone with COVID-19 symptoms, and exhorting them to click for more information.
It’s often impossible to divine who is behind such scams, although you can report any phishing texts to your cell carrier and block these numbers.
7. Consider the last time you used public WiFi
According to Kaspersky Lab, one in four hotspots are unsecured, and even the ones that are password-protected could potentially be set up by someone with malicious intent. On top of that, the protocol (WPA2 or WPA3) that encrypts traffic between devices and routers can itself be vulnerable – as in the serious WPA2 flaw uncovered by researchers in 2017 that would have allowed certain traffic to be intercepted.
If your phone isn’t protected by a VPN and you logged into an unsecured public WiFi hotspot, it’s possible someone could have been spying on the connection – and scraped your sensitive information if you logged into your email or bought something online.
8. Is your iCloud safe?
iPhone user? A cracked iCloud login can allow someone to not only access your photos, but also make use of semi-legal spy software to remotely monitor your device’s calls, messages, contacts and location.
Shows Wrong Device Name Mac Hacked Download
Luckily, enabling two-factor authentication for your Apple ID drastically reduces this risk, because if someone tries to sign into your account from a new device, you’ll receive an approval request and sign-in code on your iPhone (or other iOS/Mac devices linked to your Apple ID).
(To enable two-factor authentication, for iOS 10.3 and newer: Settings > [your name] > Password & Security. For iOS 10.2 or older: Settings > iCloud > Apple ID > Password & Security.)
However, a weak or reused password without two-factor authentication can put your account – and phone – at risk.
Here’s how it works: Many people use the same email address in their Apple ID as the login for dozens of online accounts. If this email address is revealed in a data breach, then hackers – who may purchase or find these login details at data dump websites – have access to your Apple ID.
Couple that with a weak password and your iCloud account can be breached by attackers who use cracking software to guess hundreds of hacked or common passwords in order to breach accounts.
Unfortunately, the same goes for an email and password combo that can be guessed or found out by someone you know who’d want to spy on you – especially if they can access your iPhone to use the two-factor code.
9. Run a security scan
Since most malware is designed to evade detection, you may not discover much on your own. Spyware apps – or stalkerware – is one category of particularly insidious apps designed purely to monitor a victim’s activity (rather than for any financial gain).
Security apps, particularly for Android, can help determine if your phone contains such a malicious app, as well as help fend off future cyber attacks by, for example, preventing you from visiting malicious webpages.
Android: Commercial spyware is unfortunately all too easy to find online. Such spy apps have system-level access to extremely detailed information about your device activity such as the messages you write, photos you take and GPS location – and what’s more, these apps are hidden from view.
They also need to be downloaded physically to your device, which means if they’re on your device it was done by someone with access to your device (and your PIN). Chances are, you can figure who in your life would want to monitor your phone.
To find out if you have such apps on your Android phone, download a security app such as Bitdefender or McAfee, which will flag any malicious programs. You can also head to Settings > Security > Device administration and check if “Unknown sources” for app installations is enabled (and you didn’t do it) – this allows apps from non-official app stores, on which there’s likely to be far more stalkerware.
iPhone: Spy apps on a non-jailbroken iPhone are far less prevalent since such software – which tampers with system-level functions - doesn’t make it onto the App Store. (However, they do exist and work via someone knowing your iCloud login and password.)
If your iPhone is jailbroken, that opens it up to potentially malicious apps that haven’t been vetted by the App Store, including spy apps downloaded without your knowledge.
Security apps such as Lookout and Sophos will alert you if your iPhone has been jailbroken – so if you’re alerted of this but haven’t done it yourself, that can be a red flag.
However, whether security software – for Android or iOS – can find spy apps will depend on how sophisticated or new the spy app is since security software scans for malware that’s already known. (That’s why it’s crucial to download updates to security software as soon as available since updates will incorporate new instances of discovered malware.)
3 steps to take if your phone has been hacked
1. Delete any apps or messages that may be malicious
If deleting them fixes any performance issues, great. Even if not, it’s a good idea to clear your device of apps that may have been flagged from that security scan.
You can also try shutting down apps one by one, as soon as your phone starts to slow down or heat up. If shutting down a particular app seems to return things to normal, that app may be malicious – or at the very least, not play too well with your device.
2. Do a factory reset
If after deleting the suspicious app(s) your phone is still behaving strangely, this nuclear option is a quick way of clearing your device of malicious – or sluggish – software left behind.
Android: Settings > System > (Advanced) > Reset options > Erase all data
iPhone: Settings > General > Reset > Erase All Content and Settings
3. Check if your information is out there
Unfortunately, many hacks and malware present few to no symptoms and often the only time people are aware of a breach is when their digital services are hacked, or, worse, they’re the victims of identity fraud, where hackers have used their stolen information to open accounts or lines of credit.
There are a few tools you can use to check if any of your information has already been compromised. Have I Been Pwned? is a website run by security developer and Microsoft Regional Director Troy Hunt that checks if email addresses have been exposed in breaches of popular apps and services.
Security apps including Bitdefender (Android) and Lookout (iOS) can also alert you if apps and services you use have been breached, putting your personal information at risk.
Depending on the scale of the data that has been exposed, you may want to set up a fraud alert at the major credit agencies, which will require any potential creditors to request additional verification of your identity.
Keeping your smartphone safe
If you find that your logins – particularly passwords – are floating around online, the first thing to do is to change your passwords. The best way to do that is to use a password manager which can automatically generate and save complex, unique passwords for each of your accounts. Check out our top-rated picks here. We like the Dashlane password manager, whose Premium version (from $4.99/month) also scans the Dark Web for instances of your emails or logins being posted for sale.
And to reduce the risk of future phone hacks, always observe general cybersecurity hygiene:
- Think twice before clicking links in SMSes, other messages and emails
- Review app permissions to minimize the risk of a malicious app download.
- Enable two-factor authentication for every online account possible – and especially primary emails and logins like your Apple ID.
- Download security updates for your phone when available to patch vulnerabilities that could otherwise be exploited.
- Protect your device with a PIN or biometric authentication.
Updated on 6/16/2020 with new tips and recommendations
[Image credit: phone hacker concept via BigStockPhoto]
Smart hackers don’t get caught. They break into your device, steal everything they can, and finish without a trace. Sometimes they leave a trail of destruction in their wake – malware, weird ads, confused relatives, and even a drained bank account or stolen identity.
It’s pretty easy for hackers to do their job. Most people are ambivalent, but you don’t have to be. Click here for 5 security mistakes you’re probably making right now.
Computers, phones, routers, and down to the innocent webcam are vulnerable to cyber-criminals. So what if they’ve already broken in, yet you don’t even know they’re there? Here are clear-cut signs that you've been hacked.
1. Your gadget suddenly slows down
One of the side-effects of malicious software is a slow gadget. Software gets sluggish, or constantly freezes, or even crashes. If you start noticing some of these symptoms, your gadget may very well be infected with viruses, trojans or worms.
Malicious software usually runs in the background, secretly eating up your gadget's resources while it's active.
Here are tools you can use to pinpoint those nasty applications. If an application that you don't recognize is hogging your computer resources, it's likely a virus.
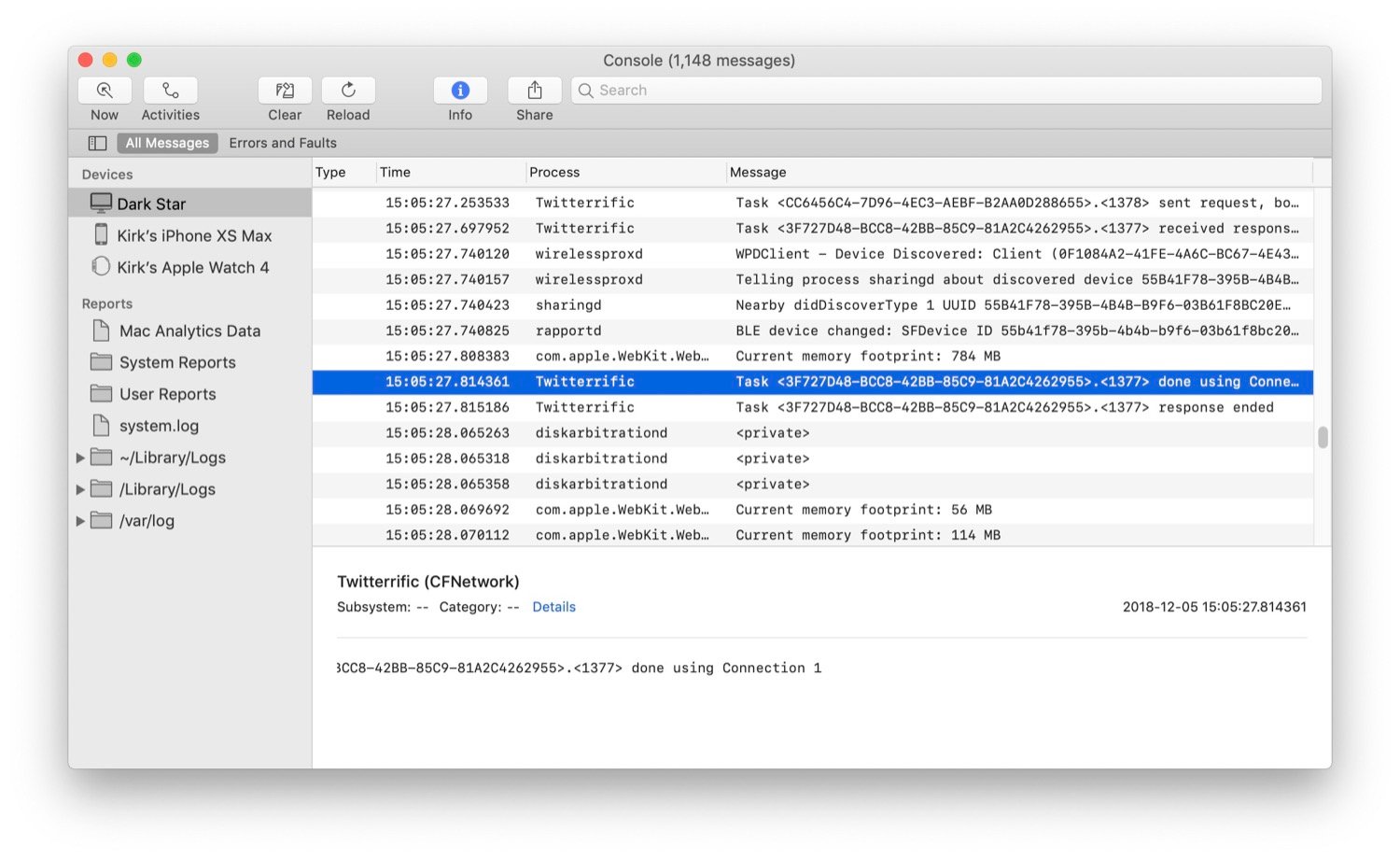
PC: Use Task Manager
There are a few ways to see what processes your computer is running. The easiest is to bring up Windows' built-in Task Manager. Just use the keyboard shortcut CTRL + SHIFT + ESC and go to the Processes tab.
Put simply, the Task Manager lists all of your computer’s current tasks and how much processing power they’re using, measured in Central Processing Units (CPUs). Open up Task Manager and check the CPU and memory columns for each process.
You might find one process is using 100% — or close to it — of your CPU. Open up the program associated with the process and see what it's doing. Restart the task and monitor it, but this program might be the culprit.
Click here to learn powerful Windows Task Manager secrets for diagnosing and repairing slow computers.
Mac: Use Activity Monitor
The Mac equivalent to Task Manager is its built-in Activity Monitor. The quickest way to access the Activity Monitor is by using Spotlight Search.
Click the magnifying glass on the right side of the menu bar at the top of your screen, or press Command + Spacebar to open a Spotlight window and start typing the first few letters to auto-complete 'Activity Monitor.' Just press Enter to access the tool.
Similar to Window's Task Manager, Mac's Activity Monitor displays a list of all your open processes with tabs for CPU, Threads, Idle Wake Ups and Network usage.
Learn these three troubleshooting Mac shortcuts the pros use.
If this happens when you are on an iPhone, try a soft reset by holding the power and the home button until it reboots with the Apple logo. This step can clear out frozen apps that can be hogging your memory.
2. You’re using way more data than usual
Every Internet provider has tools that can keep track of your monthly bandwidth consumption. Look at Data Usage Meter or Data Monitor, depending on your provider. Compare the amount of data used from the prior months, and if you notice sudden spikes in your data activity even though you haven't changed your patterns, then chances are you are infected.
For example, adware infected gadgets usually perform unsolicited clicks in the background to generate profit for cybercriminals. These stealthy tactics use up bandwidth and the unauthorized data they consume should be fairly easy to spot.
Do you want to save on your data consumption? Here are 5 steps to cut your data usage in half.
More Komando: How to find everything Microsoft knows about you
3. Videos suddenly buffer and web pages take forever to load
When a streaming video suddenly freezes, and your device appears to be “thinking,” this is called buffering. This annoyance often happens, especially if you play a lot of videos or your Wi-Fi connection is weak. If it’s happening a lot, or videos fail to play at all, you’re wise to suspect neighbors are piggy-backing on your connection. Click here for steps on how to check for Wi-Fi thieves.
Then again, malware can also slow down your Internet traffic by DNS hijacking. In short, hackers can redirect your Internet traffic to unsafe servers instead of the secure servers. This will not only slow down your browsing experience, it's also a serious security risk. For example, if your router's DNS settings have been hijacked, each time you visit your online bank's website, you'll be redirected to a phishing website instead.
To check your router's DNS settings, you can use an online tool like F-Secure Router. For more security, consider changing your DNS server to one with advanced hijacking protection like CloudFlare or Quad9.
Do you want to make your router hack-proof? Click here for more tips.
Shows Wrong Device Name Mac Hacked Photos
More: 6 ways to speed up slow Wi-Fi
4. Programs and apps start crashing
Now, here is a clear sign that your system has been infected. If your antivirus software and task manager are either crashing or disabled, a nasty virus has likely taken hold of your critical system files.
You may not be able to click on once-reliable apps. In the worst case scenario, ransomware may prevent you from opening favorite files.
You can try and fix the problem by booting your gadget in Safe Mode. With Safe Mode, your computer will be running with just the bare essentials. This way, you can safely delete and uninstall any programs and files that you can't during normal operation.
Windows:
On Windows, search for System Configuration then open it >> select Boot tab then tick off Safe Boot >>check Minimal (this is enough for most cases) >> click on OK to confirm >> Restart your computer.
Click here for detailed steps on how to boot into Windows Safe Mode.
macOS:
On a Mac, press and hold down the Shift key while restarting your computer. Keep holding the key through the Apple logo and release when you see the login screen.
Android:
Android also has its own version of Safe Mode but there are different ways to activate it, depending on your phone model. Click here to learn how.
iOS:
Stock iOS doesn't have a Safe Mode but you can try a soft reset to fix most issues. To do this, press and hold both your iPhone's Home button and the Sleep button at the same time, wait for it to restart then let go of the buttons when the Apple logo is displayed.
The iPhone X doesn't have a Home button so the process is a bit different. Press and quickly release the volume up button, press and quickly release the volume down button then press and hold the side button and release when the Apple logo appears.
5. You start seeing pop-up ads
Malware can also add bookmarks that you don't want, website shortcuts to your home screen that you didn't create, and spammy messages that entice you to click through. Apart from slowing down your gadget and eating away at your data, these intrusive notifications can also install more malware on your system.
Criminals can also use DNS hijacking to modify the ads that you see while browsing. Instead of the regular ads that you should be getting, they can be replaced with inappropriate or malicious ones.
On Windows, clean out adware with SpyBot Search & Destroy. On a Mac, use Malwarebytes for Mac.
6. Your gadget suddenly restarts
Automatic restarts are part of normal computer life. Software updates and new application installs can prompt you to reboot your computer. Your system will warn you when these happen, and you can delay or postpone them.
Yet sudden restarts are a different story. With Windows 10, there's a free malware detection and extraction program called Microsoft Windows Malicious Software Removal Tool.
I recommend a Full Scan with this tool to verify that your computer is updated with the latest malware definitions.
7. Unexplained online activity
Hackers covet your usernames and passwords. These details, coupled with social engineering tricks, can gain access to your banking accounts, your social media profiles, and your online services.
Keep an eye on your email's 'sent' folder and on your social network posts. If you notice emails and posts that you don't remember sending or posting, it's likely that you have been hacked.
Constantly check your accounts for unauthorized activity including movies on your Netflix profile that you don't remember streaming, mystery purchases that you haven't made, songs on your Spotify list that you didn't listen to, credit card charges that came from nowhere.
What other tech tips will help you?
Call my national radio show and click here to find it on your local radio station. You can listen to the Kim Komando Show on your phone, tablet or computer. From buying advice to digital life issues, click here for my free podcasts.